We don’t deal with outsiders very well
They say newcomers have a certain smell
You have trust issues, not to mention
They say they can smell your intentions
You’re lovin’ on the freakshow sitting next to you
You’ll have some weird people sitting next to you
You’ll think “How did I get here, sitting next to you?”
But after all I’ve said, please don’t forgetTwenty One Pilots, Heathens
Note: This article was conceptualized mid February 2018. I am reposting it here to jump-start my articles about cryptocurrency and malware for 2018.
We are seeing increase in cryptocurrency mining malware activity (aka coinminer) in the overall threat landscape scene. In the threat samples we have seen from the labs, we have observed several notable findings:
- the favorite cryptocurrency to mine/abuse is Monero (a shift from previous Bitcoin)
- the resource sought/hijacked is CPU (with some dash of GPU mining) and
- these coinminers can be generally categorized into 2 groups: scripts (web miners) and executable miners
- In the executables, Windows files dominate, with some Mac OS, and linux files from time to time
Monero, the new Cryptocurrency Mining Malware King?
What is Monero?
Monero is a cryptocurrency that promises anonymity better than Bitcoin. As per Monero website, sending and receiving addresses as well as transacted amounts are obfuscated by default. They claim that transactions on the Monero blockchain cannot be linked to a particular user or real-world identity. It is therefore logical for cybercriminals to make use of this for their activity, given the improved privacy and anonymity.
Monero can be mined machines’ CPU. Monero crypto-mining uses a compute-heavy algorithm called CryptoNight, which by design, performs to run well on consumer CPUs. As CPU is a widely available resource among consumers, distributing cryptocurrency miners covertly in desktops seems feasible for the malicious actors and using the victim’s computing power (e.g. hardware and electricity costs) is attractive as cryptocurrency mining provides a good monetization venue for their malicious campaign.
This CPU mining approach was the same one being used and abuses in the early stages of Bitcoin. I have observed that since Bitcoin CPU mining cannot be done profitably nowadays, the shift will be for more cost efficient and affordable crypto like Monero. I believe ASICs, Mining Rigs and Cloud Server Farm combo is way to go with bitcoin, but this strategy needs huge investment. Also mining difficulty for Bitcoin is so high now when compared to the early years of bitcoin.
I am also theorizing that the current price of bitcoin seems to affect cybercriminal usage, because high prices of BTC mean it is too costly to procure/exchange bitcoin thus affecting the value/profits/RoI of the activity.
My thoughts on Coinhive…
Coinhive is a website provider Monero cryptocurrency miner that you can plug and play on your website using JavaScript technology.
Coinhive works by providing website publishers a Javascript code that they can embed into their website. What this code does is that it “covertly” uses the website visitor’s CPU processing power to mine the Monero cryptocurrency. This is a good alternative for monetization of the website.
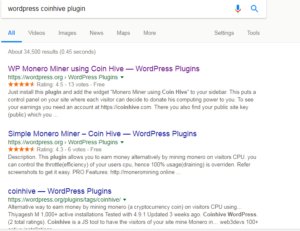
The challenge with Coinhive is that we have seen that it is heavily abused and most of the times website visitors won’t know that their CPU resource is being used without their knowledge. Scripts and website plugins are widely publicized in the internet on how easy to abuse Coinhive to force the cryptocurrency mining without user intervention.
We have seen Coinhive related infections and we can see it can be another venue for malvertising (for full story refer to this link). Take note Coinhive is not the only website providing this kind of JavaScript Monero miner via simple JS and API calls.
For more cryptocurrency mining malware insights, please read my article posted in Trend Micro Security Intelligence Blog entitled: Cryptocurrency-Mining Malware: 2018’s New Menace?
What’s Next?
I am planning to post more articles about executable coinminers, other cryptocurrency being targeted and abused, and some infosec topics and mixes soon. Watch out for it here at AVSecurityProductManager.com
Before I end this post, here are some standard disclosure/disclaimer:
I work at Trend Micro. The views expressed in this blog are mine and mine alone and do not necessarily represent my employer’s positions, strategies or opinions. Read more about me here.
If you want to get in touch, you reach me me via Twitter or Linkedin
Image credits:
Monero Logo – getmonero.org
Coinhive Logo – Coinhive website